This section is aimed at explaining what a bootloader is, why is it needed and details regarding the bootloader and bootflow used in the MCU+SDK.
Generally speaking, bootloader is a piece of software / firmware that runs as soon as you power on an SoC. A bootloader's main duty is to start the subsequent pieces of software, such an OS, a baremetal application or in some cases another bootloader. When it comes to embedded, the bootloader is usually closely tied with the underlying SoC architecture. The bootloader is usually stored in a protected, non-volatile on-chip memory. Typically the bootloader performs various hardware checks, initializes the processor and configures the SoC registers etc. Since the primary aim of the bootloader is to load the next piece of software, it needs to communicate to the external world to receive this firmware/application image. This can be over a number of protocols - USB, UART, SPI, I2C, External Flash, Internal Flash, SD Card, Ethernet, CAN etc. Bootloader is also a key component in embedded security. Hardware Root-of-Trust is usually passed onto the bootloader and is passed on down the line.
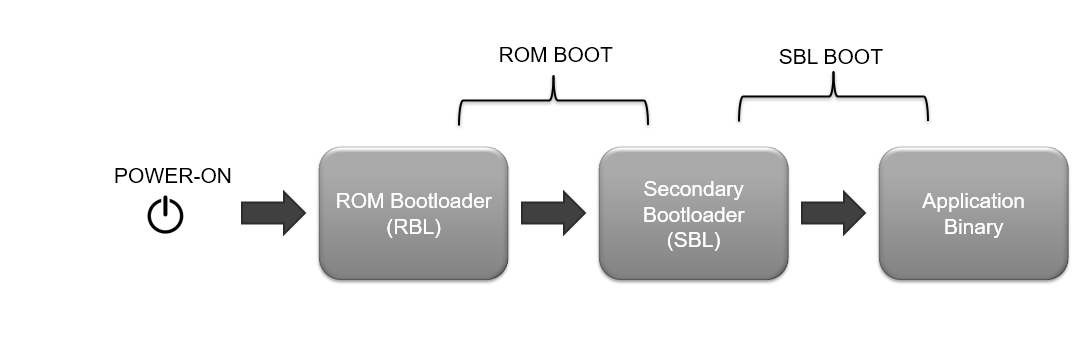
As mentioned earlier, sometimes the bootloader would be loading another bootloader which can load another one and so on. This is usually the case in advanced SoCs, and there are various reasons for this. The first bootloader is usually kept on secure, read-only memory for security reasons and to have a known state always before application software starts. It makes sense then to keep this bootloader simple and let it do only the bare minimum configuration required. This secondary bootloader can be complex and configurable to suit the needs of the application. This can also be updated easily compared to the first stage bootloader. In fact for the devices in MCU+SDK, we have a two-stage bootloading - the first stage bootloader is called ROM Bootloader (RBL) and the second stage bootloader is called Secondary Bootloader (SBL).
Multi-core bootloading is almost always a follow up when there is a multi-stage bootloading. In this case the first bootloader technically might not be even aware of the other cores, it will just boot the next stage bootloader and this second stage bootloader will take care of the complex bootloading on the different cores.
Loading a multi-core application is slightly more complicated than loading a single core application. There would be concerns regarding image preparation, shared memory access, and so on. Mostly there would be a particular format in which the individual core images are created, and then they may/may not be concatenated into a single image for SBL to load. Whatever format the application image is in, the SBL should be aware of it so that it can parse and load the image correctly.
In the MCU+SDK, the bootflow takes place mainly in two steps after you power ON the device
The RBL or ROM Bootloader is stored in read-only memory and is almost considered as part of the SoC. The details regarding the RBL and ROM Boot is out of scope for this user guide. Please refer to the Technical Reference Manual of the device for more details. But basically the ROM expects an x509 signed binary image of the secondary bootloader to be provided for boot.
The x509 template for ROM looks something like this:
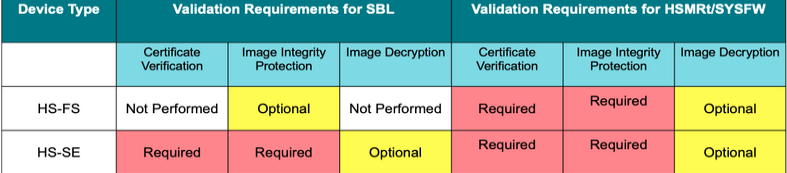
Depending on the device type, these are the validation requirements for ROM:
The SBL is like any other application, created using the same compiler and linker toolchain. It is an example implementation rather than a deliverable. It is customizable by users, but must adhere to the requirements by RBL which is a constant as mentioned above. However the steps to convert the application .out into a bootable image are different for SBL as listed below:
0x70002000 and this is the entry point for the SBL..out file is first converted to a binary format .bin using the TI ARM CLANG objcopy tool.objcopy fills the gaps with 0x00..bin file is then signed using the Signing Scripts to create the final .tiimage bootable image..tiimage file extension is kept to separate the SBL boot image from a normal application image

Now, as mentioned above, to boot an application with SBL it has to be specially prepared. Refer here Building an Application to see how an application is prepared to be bootable.
After a SBL and application image is flashed, shown below is the high level boot flow, after the SOC is powered on.
In secure device variants, there are slight differences in the bootflow. For details on secure boot, please refer Enabling Secure Boot
pBIST (parallel Built-In Self-Test) can be performed for both 200MHz and 400MHz part numbers by including the instance of mcu_bist in the sys-config for the bootloader examples. By default it's enabled only for bootloader sbl-sd. For 400 MHz part numbers ROM performs pBIST on R5FSS0 Memories and L2 Memory - Bank-0 and Bank-1. But due to ROM limitation this test is not done by ROM for 200 MHz part numbers. The mcu_bist instance can be added or removed on the basis of use-case. pBIST is perfromed only on L2 memory - three banks (Bank-1,Bank-2,Bank3 (not on Bank-0)) and R5FSS1 TCM Memories. Please refer below for more information.
mcu_bist instance will run pBIST on L2 memory - Bank 1, Bank 2, Bank 3. The mcu_bist instance can be added for sbl_qspi as it resides in Bank-0. If SBL resides in banks other than Bank-0, the pBIST setup must be updated with the specific memories.| Step | Description |
|---|---|
| 1 | SBL Startup
|
| 2 | Efuse Bit Detection
|
| 3 | pBIST Execution
|
In software workaround, pBIST is perfromed only on L2 memory - three banks (Bank-1,Bank-2,Bank3 (and not on Bank-0)) and R5FSS1 TCM Memories.
User can perfrom pBIST on the remaining L2 Memory bank-0 and R5FSS0 TCM memories on their own by following the steps given below: The following table provides an overview of the steps to perform pBIST on RFSS0 TCM and L2 Memory Bank-0:
| Step | Description |
|---|---|
| 1 | Use the SDL example of pBIST that utilizes the SDL pBIST library. |
| 2 | Set up the test environment to specify L2 bank-0 and R5FSS0 TCM memories. |
| 3 | Update the SBL to be loaded on other memory banks (excluding bank 0). |
| 4 | The SBL will load the application on the RFSS1 core, which will run pBIST on the remaining L2 bank-0 and R5FSS0 TCM memories. |
| 5 | Once pBIST is completed, the device will be reset to proceed with normal booting. |
By following these steps, you can perform pBIST on the specified L2 memory bank-0 and R5FSS0 TCM memories, ensuring proper self-testing, and allowing the device to boot normally afterwards.
• The pBIST can be run for both 200 MHz and 400 MHz part variants. To run the pBIST user can include mcu_bist instance for the specific bootloader in the syscfg.
• By default it's enabled only for bootloader sbl-null.
• The software workaround described in this user guide for L2 Memory Bank-0 and R5FSS0 TCM memories is specifically designed to address the ROM errata affecting 200 MHz R5F core variants.
• The pBIST procedure performed during the SBL startup helps mitigate the limitations imposed by the ROM.
• It is important to ensure that the SBL and associated software are correctly installed and configured on the target device for the workaround to function effectively.
To know more about pBIST and overall SDL support for pBIST, please take a look at PBIST
See also these additional pages for more details and examples about the boot flow,